Building a secure IoT device requires well-defined codes, specifications based on rigorous testing and thorough certification. OCF’s world-class security is confirmed by measuring it against several IoT security baselines developed by government and industry organizations. IoT engineers and members of the OCF Security Oversight Work Group have collaborated on the OCF specification, certification program and open source implementation, following key guidelines and mandates set forth by the industry.
The OCF Security Oversight Work Group has mapped the OCF specification to five influential IoT baselines:
- National Institute for Standards and Technology (NIST) NISTIR 8259 draft of recommendations IoT device manufacturers
- The Consumer Technology Association (CTA) C2 Consensus on IoT Device Security Baseline Capabilities
- UK’s Code of Practice for Consumer IoT Security
- European Union Agency for Cybersecurity (ENISA) Baseline Security Recommendations for IoT
- European Telecommunications Standards Institute (ETSI) Baseline Security Requirements for IoT
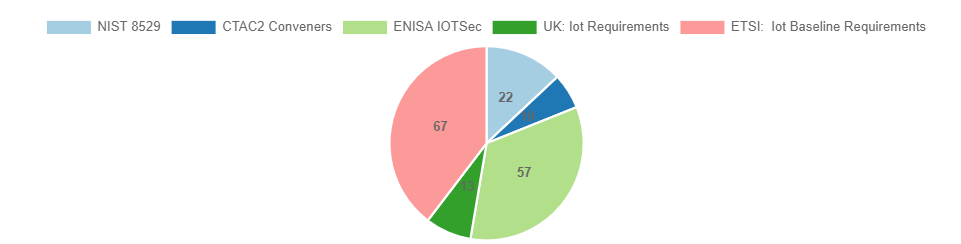
These documents give manufacturers, consumers, and the industry at-large tools to measure and validate IoT security models and specifications. The graph below highlights how many baseline capabilities are defined by each industry body.
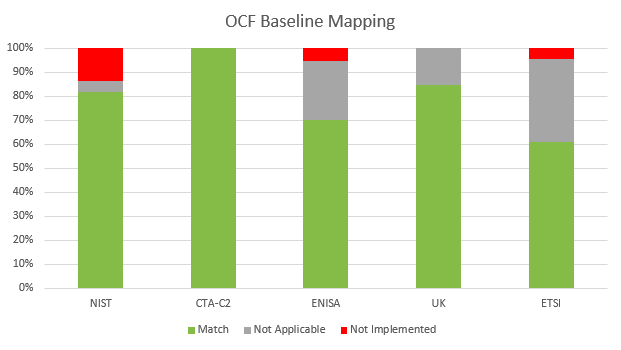
Baseline categories include trust and integrity management, strong default security and privacy, secure software and firmware updates, authentication, cryptography, access control and more. For each baseline requirement, OCF’s engineers have identified whether one or more clauses in the OCF specification meets it. Baseline comparisons that are not applicable mean that the requirement is out of scope for a device-centric specification, or the requirement is implementation/vendor specific.
OCF has outlined the percentage of required baselines our technology fulfills below:
OCF is proud to demonstrate its security capabilities and completeness of the OCF security model by meeting the above security baselines. These capabilities establish that OCF-enabled technology will maintain strong identity, encryption and confidentiality for all device traffic. Manufacturers and end-users can develop OCF products with confidence that IoT nodes will only communicate with authorized entities.
Security will always remain at the forefront of OCF technology development. To make certain the OCF specification remains in-line with the ever-changing IoT market, the OCF Security Oversight Work Group will continue to follow the security requirements put forth by the industry and government. For more detailed information on how OCF develops its specifications to industry security baselines, read Embedded.com’s article from Kyle Haefner, OCF Security Oversight Work Group Chair.
To learn more about OCF’s security approach and the specific baselines OCF maps to, visit our security page. The OCF Core Framework can be downloaded on the OCF website here.